
One of the most influential names in strategic studies is that of Colin S. Gray. He is not only an authority in the field, but a prolific writer. His book The Strategy Bridge is no less than a theoretical system which organizes the entire field, including the ranking of major theorists into tiers. Gray is no fan of John Boyd, the irascible Air Force Colonel who invented the well-known “OODA loop” but wrote nothing, preferring instead to communicate with his audience through grueling presentations rather than written works. The slides can be confusing, and the only academic treatment is Science, Strategy and War by Frans P.B. Osinga, so it is understandable that Boyd’s ideas haven’t achieved much purchase in academic strategic studies. Gray is emblematic of most authorities even though Boyd has a devoted following amongst practitioners and an annual conference devoted to his ideas. Increasingly it seems like Boyd’s ideas were quickly dismissed by strategic theory and then left behind.
Gray’s commentary on Boyd is harsh. In The Strategy Bridge, Boyd is not mentioned but is listed in the lowest tier of theorists, titled “Other Contenders.” This is not an inauspicious list as it includes Julius Caesar, Alfred Thayer Mahan, Julian Corbett, J.F.C. Fuller, and Martin van Crevald, but the ranking is conspicuously low. In Another Bloody Century, Gray is much more dismissive, writing: “…Boyd touted a tactical insight derived from personal experience of aerial combat as a general theory of conflict… A major problem with the OODA loop is that its devotees assume that a tactical insight, even principle, will be no less valid at the operational and strategic levels of warfare.” While it’s true that the OODA is at its core a tactical concept and one that ties all of Boyd’s ideas together, Boyd’s strategic ideas cannot be boiled down to just a bigger OODA loop. Still Gray, and the vast majority of the strategic studies community, stopped reading after the A.
Boyd touted a tactical insight derived from personal experience of aerial combat as a general theory of conflict.
But the most reliable test for one’s strategic ideas is history. Or in this case, history in the making. John Boyd’s ideas are evident in three modern day strategic actors and the success they’re currently enjoying is self-evident. Despite the loyalty of his acolytes, the best advocates for Boyd’s ideas are Russia, China, and the Islamic State. Each of these actors, probably without knowing it, are demonstrating Boydian strategic methods. Each of them is using an adroit mix of ambiguity, deception, distribution, and propaganda, all while demonstrating a keen awareness of the moral plane of war and warfare in a way that is serving their ends. To those of us aware of Boyd’s ideas, it comes as no surprise. Everyone else is trying to figure out if there is even a war.
Those characteristics are these. The first is ambiguity. Boyd stressed the need to act in such a way that your opponent can never really be sure exactly what it is you’re doing. Ambiguity is leavened by a healthy dose of deception. Secondly, in each case dispersion is used to increase ambiguity and deception. Even Russia has spread military units out in its eastern territory to distract. This is a violation of the classic principle of mass that US doctrine adheres to so closely. Lastly, the actions taken by these actors are aimed at achieving a mental or moral effect. While the OODA loop is a jumping off point, the essence of Boyd’s ideas is an inversion of an idea originating with Clausewitz: While the Prussian focused on overcoming friction, Boyd focused on increasing the opponent’s friction and thus using it as a weapon.Western militaries built on industrial-era ideas are even inventing the Human Domain to remind them that we are humans. Wherever you come down on whether or not war is a thing, at the very least there is strategic competition and the preparation thereof. In fact, there are three major strategic competitions occurring simultaneously, and each of them exhibit strong Boydian characteristics.
Russia: Just Say Nyet
This idea is most evident today in the case of Russia’s slow-roll invasion of Ukraine. Russia was so quick to decide and act on the opportunity offered by the Euromaidan protests and subsequent ousting of President Viktor Yanukovych that the Crimean Peninsula was annexed before western observers could decide if something was even happening. The most obvious facet of Russia’s information warfare is the denial of information about Russian troops. As recently as last month, there is still doubt in some minds as to whether Russian troops are even in Ukraine. Additionally, Russia has used military exercises in the region to distract attention from events inside Ukraine, using mass to focus attention where they want it. This method has numerous effects: It trains Russian units, it distracts western and Ukrainian audiences from focusing on the fighting in Ukraine, and intimidates Ukraine and other countries in the region.
Russia is also concurrently conducting cyberwarfare methods to aid in distraction as well as intelligence collection. Russian propaganda efforts include the manipulation of history, threats, straight-forwardmisinformation, and the timeless art of trolling. Importantly, Russia has made a concerted effort to undermine the morale and cohesion of the Ukrainian military by placing agents within it, so much so that it may complicate Canadian plans to provide advisors to the Ukrainians.
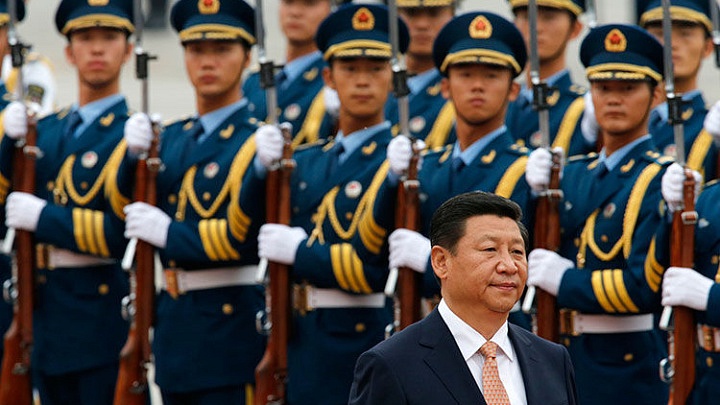
China: Nine Dashed Smoke Screen
In the case of China’s efforts to secure greater control over the South China Seas, it uses many of the same methods. At the Naval War College’s 2014 Current Strategy Forum, the Vice Commandant of the US Coast Guard, Vice Admiral Currier, said this: (quoted in this post on Chinese efforts in the South China Sea by Matt Hipple at War On The Rocks)
We see China, in the disputed claims area, using what is now called the coast guard. They took four or five maritime governance organizations, and in a course of a couple of months, painted all the ships white and put a stripe on them, and now it’s called the China Coast Guard. What’s the maneuver there? Is it a soft-power application? Is it a part of their maritime portfolio that we should be aware of?
In a move straight out of The Art of War, China has taken advantage of American views on the role of a Coast Guard (law enforcement except during times of war) to camouflage the fact that they essentially militarized previously non-military assets. China is also attempting to extend its territory in two ways: building oil rigs in disputed waters and building new islands in disputed waters. These efforts will have the effect of establishing de facto Chinese control. Meanwhile, they prevent interference with these efforts through minimal means, using water cannons to fend off Vietnamese boats so as not garner more publicity. By the time a concerted effort on the part of other actors in the region to prevent Chinese encroachment, it will already be a fact and thus harder or impossible to reverse. China is evenproducing globes that include the disputed Nine Dashed Line which demarcates the area to which they lay claim, fostering in the minds of various audiences that the territory is Chinese.
Despite the loyalty of his acolytes, the best advocates for Boyd’s ideas are Russia, China, and the Islamic State.
The Trick of ISIS
In ancient Egyptian mythology Isis used a particularly violent trick to force Ra, the Sun God, to tell her his secret name. She caused a snake to bite him and refused him the antidote, which only she possessed, until he relinquished his secret.
The organization that bears her name is by chance is no less willing to use deception and violence to accomplish its aims. Early in its campaign in Raqqa, Syria after infiltrating a small group of fighters into Syria from Iraq, Islamic State intelligence operatives convinced each rebel group that only other rebel groups would be attacked, disabling a potential rebel alliance against the Islamist group. Until various rebel groups banded together to attack the ISIS fighters in late 2013, this tactic of divide and conquer worked. Upon losing ground to the rebels, ISIS fighters dropped their trademark all black uniforms, adopted the casual civilian clothes of the rebels, and then surprised a rebel group in an attack. The confusion sown by the uniform change collapsed the rebel unity.
In Iraq, ISIS used a tightly-planned shaping campaign to undermine the morale and cohesion of the Iraqi Army before beginning its major offensives. From mid-2013 to mid-2014, ISIS assassinated key leaders in the Iraqi Army both on and off duty, employing both IED attacks and ambushes with small arms. When the conventional offensives against Mosul and other parts of Iraq began, the weakened Iraqi Army- susceptible to the fear of ISIS’ reputation- collapsed. By applying fear over a period of time and then a catalyst, they tricked the Iraqi Army into giving up Mosul without a fight. This campaign to undermine the moral foundation of targeted Iraqi Army units could have been lifted right out of John Boyd’s slides.
In another example, ISIS executed a captured Jordanian Air Force pilot by immolation, an act that shocked the world. In response, Jordan executed two ISIS-connected prisoners of its own. While both prisoners were previously tried and sentenced to death, the knee jerk reaction on the part of Jordan certainly looked like a country that had sunk to its enemy’s level. In one slide presentation, Boyd recommended that one should “sever [the enemy’s] moral bonds.” Inducing a country to truncate its professed due process is one way to do that.
The Islamic State’s fearsome reputation, carefully incubated by ISIS’ sophisticated media arm and iconography down to their black “ninja” style battle outfits, is thus a weapon. This is not a new phenomenon. Entire armies crumpled rather than face the Mongol hordes- another group that cultivated a reputation of fear. Mongol massacres were calculated demonstrations intended to convince the inhabitants of cities to capitulate rather than endure a siege. This was a compensation for early Mongol weakness in seigecraft. The brutality of the Islamic State is a similar, calculated tactic.
Circling Back to Boyd
These efforts at deception and ambiguity may have the effect of hacking the OODA Loop of strategic opponents like the United States. By the time their opponents realize the danger, these actors have already decided and acted. They’re not just out-cycling their opponents; they’re stealing a march and getting a head start.
A simple recitation of one of Boyd’s slides where he summarizes recommendations suffices to demonstrate the similarities:
Probe and test the adversary to unmask strength, weaknesses, his maneuvers and intentions.
Employ a variety of measures that interweave menace, uncertainty and mistrust with tangles of ambiguity, deception and novelty as the basis to sever an adversary’s moral ties and disorient or twist his mental images and thus mask, distort and magnify our presence and activities.
Select initiatives and responses that are least expected.
Exploit, rather than disrupt or destroy those differences, frictions, obsessions, etc., of adversary organism that interfere with his ability to cope with unfolding circumstances.
Subvert, disorient, disrupt, overload or seize vulnerable and critical connections, centers and activities that provide cohesion and permit a coherent OODA cycle in order to dismember the organism and isolate remnants for absorption or mop-up.
The second bullet describes Russia’s actions in Ukraine almost perfectly. The Islamic State’s Mosul campaign resembles the last bullet so much that one would not be surprised if Boyd planned it himself.
In a further summarization in his presentation titled The Strategic Game of ? and ?, a more obscure work than his famous Patterns of Conflict, Boyd described the art of success as, “Shape or influence events so that we not only magnify our spirit and strength but also influence potential adversaries as well as the uncommitted so that they are drawn towards our philosophy and are empathetic toward our success.” Vladimir Putin’s domestic approval ratings have skyrocketed since the Ukraine crisis began. The fact that China is literally reshaping the South China Sea with artificial islands sends a powerful message to other region actors. Despite their savagery, the Islamic State continues to attract followers from all over the globe.
The strategic ideas of John Boyd, long dismissed by the academic strategic theory community, are unfolding before our eyes. Importantly, Boyd did not portray the use of these tactics alongside more “conventional” tactics as some unique new way of war like hybrid, asymmetric, or fourth generation. His vision was simply warfare as it has always been waged. It is only surprising to those who have ignored the prevalence of such methods in history.
Boyds Revenge
John Boyd’s ideas have been widely available, for free, for decades but his name remains unmentioned even as those ideas play out in events. One possible conclusion from these trends is that since the United States has invested so heavily in being able to fight and win a large-scale conventional war that it stopped innovating in other forms and areas of warfare. Since the US cannot be challenged in conventional warfighting, other strategic actors innovated in the opposite direction. This is something that General Mattis has warned about. Warnings about the US military becoming a “Hollow Force” have become more frequent in recent years. The typical definition of a hollow force is one that exists on paper with appropriate systems but is untrained and undermanned. Another definition could be a military that is manned, trained, and resourced but is unfamiliar with and unable to fight the wars it will be confronted with. One example is the Prussian Army under Frederick William III- steeped in the traditional training and discipline instilled by Frederick the Great- that was dissected by Napoleon at Jena-Auerstadt and during the following retreat.
One way that the United States can counter these methods, especially in the case of Russia, is to use information gathered by its extensive intelligence apparatus not just for decision-making but as a way of developing a counter narrative. The Western media does a passable job of this on its own, but surely has less information about Russian activities in Ukraine than does US intelligence. Since the US classification system prevents the dissemination of information- even about adversaries- the US government would have to orchestrate a coordinated series of leaks of classified information to develop a counter narrative and to undermine the narrative being presented by Russia. As it stands now, the United States is simply not a player in the battle of the narrative playing out over Ukraine.
One way the United States should not utilize information is to refute rumors of an enemy leader’s wounding that could undermine the morale of his organization. Let them worry.
In any event, it is high time the ideas of John Boyd got another look by strategists and practitioners alike. Writers like Emile Simpson and General Rupert Smith have written works regarding modern warfare in the information age. The New America Foundation has organized The Future of War Project in an attempt to ascertain future trends in war and warfare. The military is always planning ahead, as shown by documents like Expeditionary Force 21 and Win in a Complex World 2020–2040. But as so many thinkers look ahead for answers, they may miss what’s behind them.
This post originally appeared in The Bridge (@Strategy_Bridge) on 1 June 2015.
[Top Photo: Flickr CC: Airwolfhound: A flight of U.S. Air Force F86 Sabres; Body Photo: Wikipedia: ChaoticLogic]

Boyd recommended that one should “sever [the enemy’s] moral bonds.” Inducing a country to truncate its professed due process is one way to do that. And we have GITMO, secret no-fly lists and the USAPATRIOTACT, albeit slightly watered down, thanks to Rand Paul.